
Publication
Senate Bill 29 on track to further Texas’ push as business hub
The Texas Business Court was established as a specialty court to handle complex business disputes on June 9, 2023, through the passage of H.B. 19.


Global | Publication | August 2017
Global supply chains and secure technology are two of the pillars sustaining our fast-moving, interconnected world. As such, not only are they critical to global business operations, but they are also a high-value target for hacktivists and cyber criminals.
While cyber risk has been an area of focus for risk officers and general counsel for a long time, the scope is often limited to first-party exposure: attacks against a company’s IT infrastructure, malware and data breaches are all viewed through a first-person lens. Nevertheless, four of the most highly publicised cyberattacks and data breaches of the past years have been perpetrated by infiltrating a supplier’s network, and using it as a gateway to the target’s systems. Retailers Home Depot and Target have been subjected to major data breaches as a result of hacks into third party systems, as were the U.S. Office of Personnel Management and security vendor RSA. More recently, the software update mechanism of a popular accounting software used in Ukraine is claimed to be the source that enabled the “NotPetya” malware to spread to users of the accounting software.
These high-profile cases underline the importance of viewing cyber risk holistically, rather than as an isolated event, and of integrating supply chain exposures into the overall risk management strategy.
Regulation is evolving in response to the increasingly complex cyber risk landscape, with Australia recently modifying the Privacy Act to add a mandatory obligation to notify affected parties in respect of certain data breaches, including data breaches in third party suppliers. Starting on 22 February 2018, companies active in the Australian market will need to enhance their scrutiny of suppliers’ activities in order to mitigate the risk of cyberattacks and data breaches.
This is another reminder of the importance of managing supply chain risks smartly; similar legislation around the globe already addresses liability for acts of money laundering, terrorism financing, corruption and bribery and human rights abuse. Companies relying on complex, global supply chains should act sooner rather than later to manage cyber risk across their supply chain, and to thoroughly prepare for potential incidents and regulatory developments.
Cyber incidents can occur at any point along the supply chain, and have multilayered consequences. Our legal and technology experts have put together four risk scenarios that are likely applicable to most companies reliant on global supply chains.
Every business can, and should, conduct a similar exercise in order to test its own, and its supply chain’s, resilience to potential cyber incidents, and prepare their crisis management and recovery strategy accordingly.
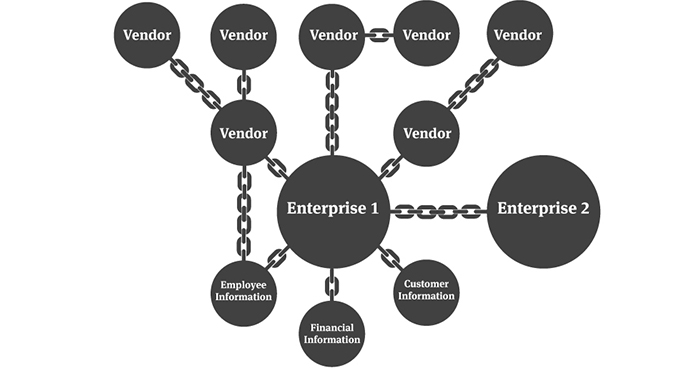
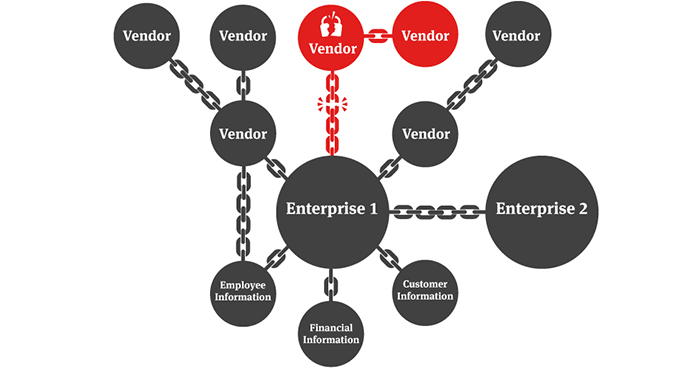
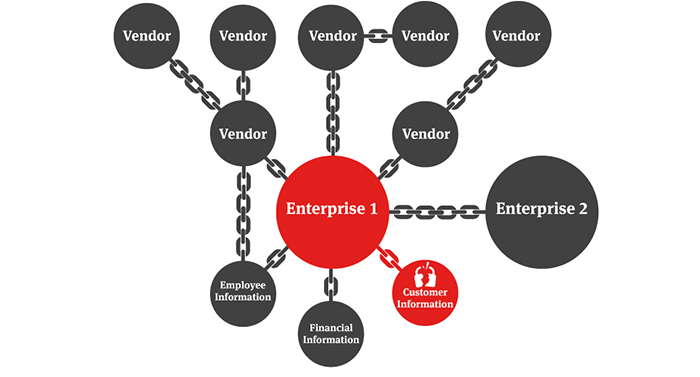
The lesson from the above scenarios is clear: the cybersecurity of a supply chain is only as strong as its weakest link, and a security breach in any part of the supply chain will likely have an adverse impact on the rest of the supply chain. It is therefore prudent to consider and manage cyber risk in a holistic manner, looking well beyond the boundaries of your own systems. It is also critically important to ensure that your organisation is not the weakest link in the supply chain.
Knowledge and preparation are key to protecting against cyber incidents and managing them successfully when they occur. Many businesses are already conducting audits of their supply chains, and tracking vendor data over the years. Amongst the key actions to take in order to identify cyber risk across your supply chain, quantify the potential consequences of an attack, and prepare for the possibility of an incident, are:
Former FBI director, Robert S. Mueller, III, once said that there are only two types of companies: those that have been hacked and those that will be. Taking into account the magnitude of the global market for stolen credit card data, estimated at US$114 billion, the prospects of any company escaping the attention of hackers look bleak indeed.
However, businesses are taking a proactive stance, and building resiliency against the threat of cyberattacks. Well-established crisis management policies and processes, together with a tried and tested business continuity plan that addresses supply chain breaches and contingencies, can make the difference when facing a large-scale cyber incident.
Transferring risks through cyber insurance is another strategy employed by an increasing number of companies. Care should be taken with regard to the exact coverage supplied by policies, in order to ensure that extensions apply to breaches across the supply chain, rather than limiting coverage to first-party risks. Insurance can also be a useful tool in vetting suppliers, given that the application process for cyber coverage is usually thorough, and will provide an additional safety net in case of a breach. A significant challenge in arranging for cybersecurity insurance is to quantify the exposure and potential loss. Target in the US found this out the hard way, as a US$50 million cyber insurance policy was estimated to only cover 25 per cent of the cost of the data breach that it suffered in 2013.
Cyber risk is part of the new business reality, along with complex supply chains and an ever-expanding technology infrastructure. In order to manage cyber risk smartly companies need to keep the security of their supply chains in mind, and to ensure that at the very least they are not the weakest link in the chain.

Publication
The Texas Business Court was established as a specialty court to handle complex business disputes on June 9, 2023, through the passage of H.B. 19.

Publication
The Texas Business Court has repeatedly held that it lacks subject-matter jurisdiction to hear cases first-filed before September 1, 2024—regardless of the procedural posture by which the case arrived at the Business Court.
Subscribe and stay up to date with the latest legal news, information and events . . .
© Norton Rose Fulbright US LLP 2025